When you’re thinking about enabling collaboration with external/third party users in your organisation’s Office 365 tenant, there are a lot of things you need to think through, agree, and design around. These include:
- Which applications will you allow external sharing in (SharePoint Online, OneDrive for Business, Office 365 Groups)?
- Will you enable member sharing, or require site owner approval when content is externally shared?
- Will you enable or disable anonymous links?
- How/where will you use domain restrictions?
- Is there anywhere you’ll disable external sharing completely?
- How will you encourage users not to share content with consumer identities?
- What processes will you put in place to manage/maintain external user permissions and guest invites?
- How will you tweak your IA (information architecture) to encourage good practices for external sharing/permissions management, e.g. sharing at the site/library level rather than per document?
- Will you enforce MFA (multi-factor authentication) on guest users?
- And lastly, but perhaps most importantly, will you use Azure AD B2B Collaboration or the traditional SharePoint Online external sharing model?
Now though, there’s one more thing you can add to that list: Per-Group Sharing Controls.
This new feature – which hits first release tenants in June 2017 – will give Office 365 administrators a little bit of extra control over who and how information can be shared with external/third party users in SharePoint Online and OneDrive for Business.
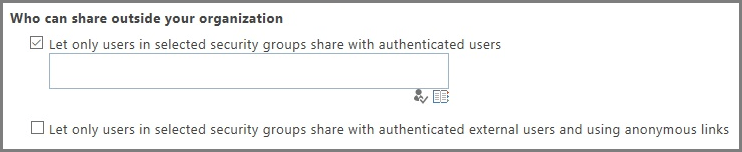
There are two new settings, the details of which I’ve lifted from Microsoft’s blog post on the subject:
- Let only users in selected security groups share with authenticated external users – With this option, you can specify one or more Office 365 security groups which contain the users who you want to allow to share with authenticated external users. Users in these security groups will not be able to send anonymous links.
- Let only users in selected security groups share with authenticated external users and using anonymous links – With this option, you can specify one or more Office 365 security groups which contain the users who you want to allow to share with authenticated external users and by using anonymous links. (This option doesn’t appear unless you have enabled anonymous access links for the tenant.)
The current set of options that the Per-Group Sharing Controls build upon are relatively coarse. The options available are: external sharing is disabled completely; external sharing with anonymous links is enabled; external sharing with only authenticated users is enabled; and sharing with users who already exist in your organisation’s directory (AKA the Azure B2B option). These options are available at both the tenant scope and site collection scope, though the site collection settings cannot be less restrictive than those defined at the tenant level (i.e. most restrictive setting wins).
The new functionality gives some extra granularity on top of these existing settings. You now have three separate audiences of users that can have different levels of external sharing ability:
- Users who are unable to share content externally (by virtue of not belonging to a group specified for either option);
- Users who can share authenticated links; and
- Users who can share authenticated links and anonymous links.
But unfortunately, the feature can only be defined at the tenant scope, not per site collection. How it’s going to play with the existing set of options is also slightly unclear at the time of writing, but I’ve been informed that the site collection settings will take precedence. For example, if anonymous sharing is disabled at the site collection level, even users in the security group that can share anonymous links will not be able to do so in that site collection. This suggests that the best way to get set-up for these new controls is to allow anonymous sharing in each site collection in all but exceptional circumstances, and control who is actually allowed to undertake this action via the new Per-Group Sharing Controls.
Also worth noting here that this new feature only covers security groups (i.e. the thing that would once have been defined as a mail-enabled distribution list). It doesn’t cover Groups, as in, Office 365 groups. Confusing, but an important distinction.
It will be interesting to have a play with these new settings when they start rolling out, but for now, it’s one more thing to consider when you’re setting up your organisation for collaboration with third parties.